Introduction
Trezor is widely recognized as one of the most secure hardware wallet solutions for storing cryptocurrency. The Trezor login process plays an essential role in maintaining that high security standard. Unlike traditional online logins, Trezor uses a hardware-based authentication method that eliminates the vulnerabilities associated with usernames, passwords, and cloud-based credential systems.
With more people turning to digital assets, the need for secure, reliable, and transparent login solutions has never been greater. Trezor provides a unique approach by requiring physical verification through a device that stores keys offline. This means that even if your computer is infected with malware or targeted by phishing attacks, your crypto remains protected.
How Trezor Login Works
Trezor login begins when you connect your Trezor hardware wallet — either the Trezor Model One or Trezor Model T — to your computer or smartphone. Once connected, you open the Trezor Suite app, the official interface for managing your crypto assets. The app immediately detects the device and prompts you to authenticate.
The first step of the login process involves entering your PIN. Unlike traditional passwords that you type directly onto your keyboard, Trezor uses a secure PIN-entry method that keeps the PIN hidden from your computer. This prevents keyloggers or malicious software from intercepting your login details. Because the PIN is known only to the user and the device, unauthorized access becomes extremely difficult.
Passphrase Protection
For additional security, users may enable a passphrase. This optional feature adds an extra “layer” to your wallet, effectively creating a hidden account accessed only by entering the correct passphrase. Even if someone gained control of your hardware device and guessed your PIN, they would still be unable to access your crypto without the correct passphrase.
The passphrase works similarly to a 25th recovery word and is never stored on the device. This means only the user ever knows it, adding another strong barrier against unauthorized access.
Why Trezor Login Is Different
Many crypto platforms rely on cloud infrastructure to store account credentials. This exposes users to risks such as hacks, phishing scams, and data breaches. Trezor avoids these issues entirely by removing online logins from the equation. Every authentication step takes place locally and requires direct interaction with the hardware wallet.
Because your private keys never leave the device, they cannot be copied, stolen, or intercepted by attackers. This offline model is the core of Trezor’s security philosophy and one of the reasons it remains one of the most trusted wallet solutions in the crypto industry.
Trezor Suite — Where You Access Your Wallet
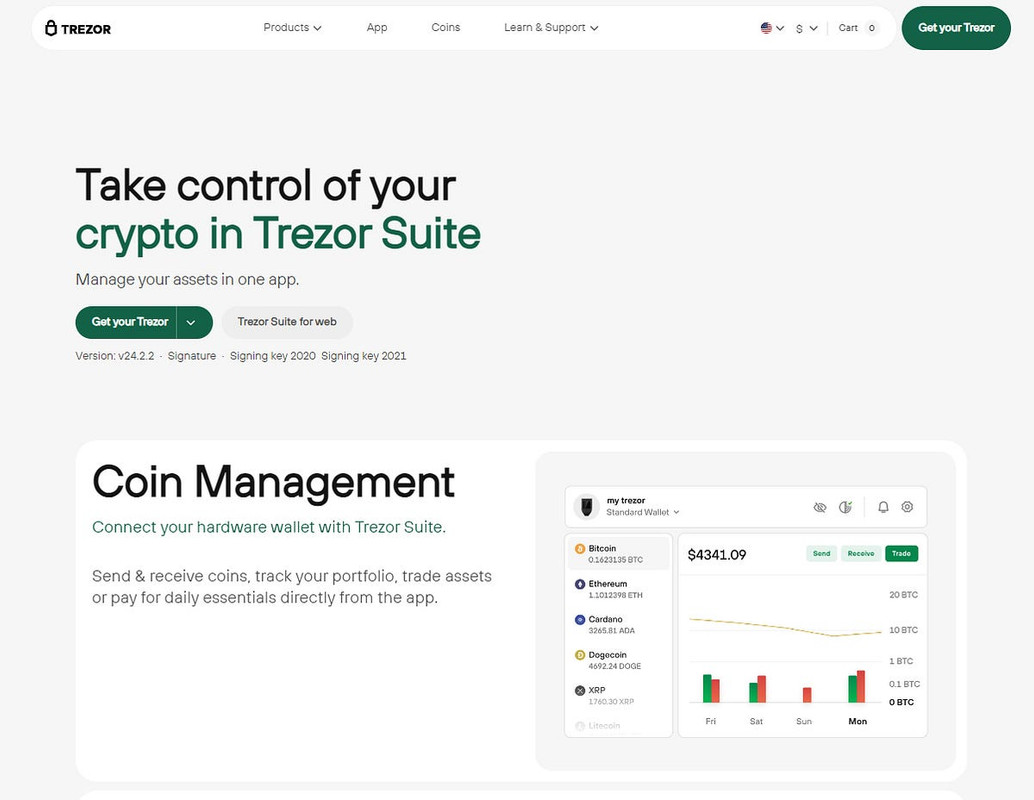
Trezor Suite is the official application used to manage your hardware wallet. It allows you to view your holdings, send and receive coins, install coin-specific apps, monitor market activity, and manage multiple accounts. The interface is clean, intuitive, and designed with security as its top priority.
Available as both a desktop application and a web interface, Trezor Suite provides flexibility while still maintaining strong security practices. The desktop version offers the highest level of protection, as it eliminates exposure to certain browser-based vulnerabilities.
Steps for Logging in Securely
Here is a simplified step-by-step guide for performing a Trezor login:
- Connect your Trezor device using the USB cable.
- Open the Trezor Suite desktop or web application.
- Allow the app to detect your device.
- Enter your PIN securely on the Trezor device interface.
- Enter your passphrase if enabled.
- Begin managing your crypto in the Trezor Suite dashboard.
Every interaction requires confirmation on the device, ensuring that no unauthorized actions can take place without your physical approval.
Security Advantages of Trezor Login
Trezor’s login process offers several security benefits that are unmatched by software wallets or online account systems:
- Offline authentication: No data is stored online or transmitted over the internet.
- Physical confirmation: All actions require approval on the device itself.
- Protection from malware: PIN entry is shielded from keyloggers and viruses.
- No cloud credentials: Eliminates risks associated with password leaks.
- Optional passphrase: Creates hidden, independent wallet instances.
- Secure element chip: Prevents tampering and unauthorized access to private keys.
Together, these features make Trezor one of the most secure options for managing digital assets.
Best Practices for Trezor Login Security
While Trezor provides robust protection, users should follow good security habits to maintain complete safety. Always download Trezor Suite from the official website, keep your device firmware updated, and never type your recovery seed into any computer or online form.
Store your recovery seed in a secure offline location, and consider using a passphrase for an extra layer of protection. Avoid connecting your Trezor to unknown or untrusted devices, and always verify transaction details on the device screen before confirming.
Conclusion
The Trezor login system provides exceptional security thanks to its offline authentication model, hardware-based PIN entry, and optional passphrase protection. By requiring physical verification and isolating private keys from the internet, Trezor offers a level of safety far beyond software wallets and online exchanges.
Whether you are new to cryptocurrency or have years of experience, Trezor ensures that your digital wealth remains private, secure, and under your full control. With Trezor Suite and its hardware login process, protecting your assets becomes effortless, intuitive, and incredibly safe.